SECURE BY DEFAULT
Console's architecture prioritizes security without sacrificing flexibility.
Conservative defaults
Console defaults to secure configurations across every product primitive. Teams can intentionally relax controls where a specific workflow requires it.
Opt-in capabilities
Connecting an integration never automatically enables its automations. Admins retain full audit and oversight, with human approval built into every AI flow.
Granular controls
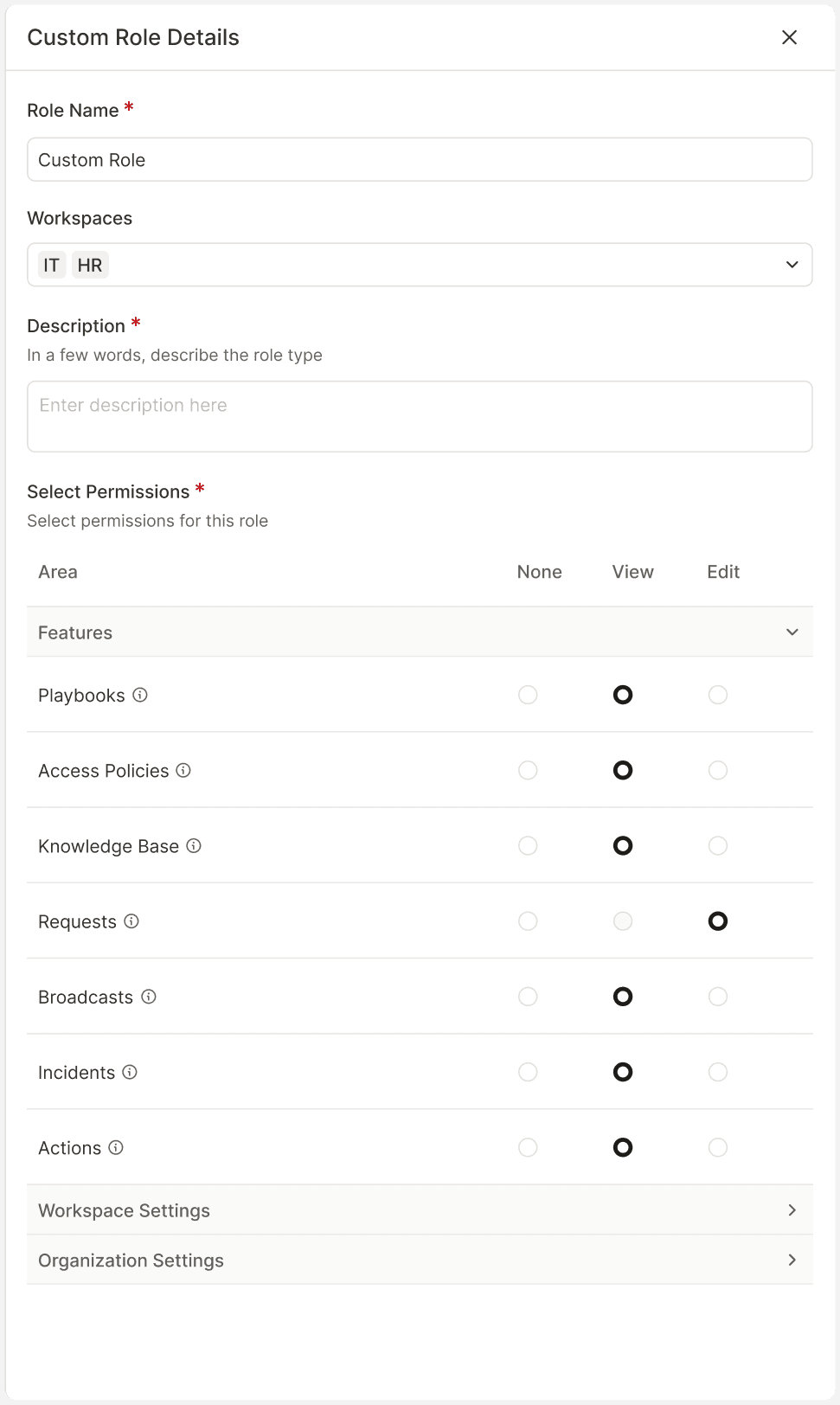
Console gives admins custom roles and fine-grained permissions across every team and workflow, so the right people have access to exactly what they need.
Build fully custom roles with appropriate permissions. Configure read/write access to all admin functionality and allow IT admins to support other teams without sharing credentials.
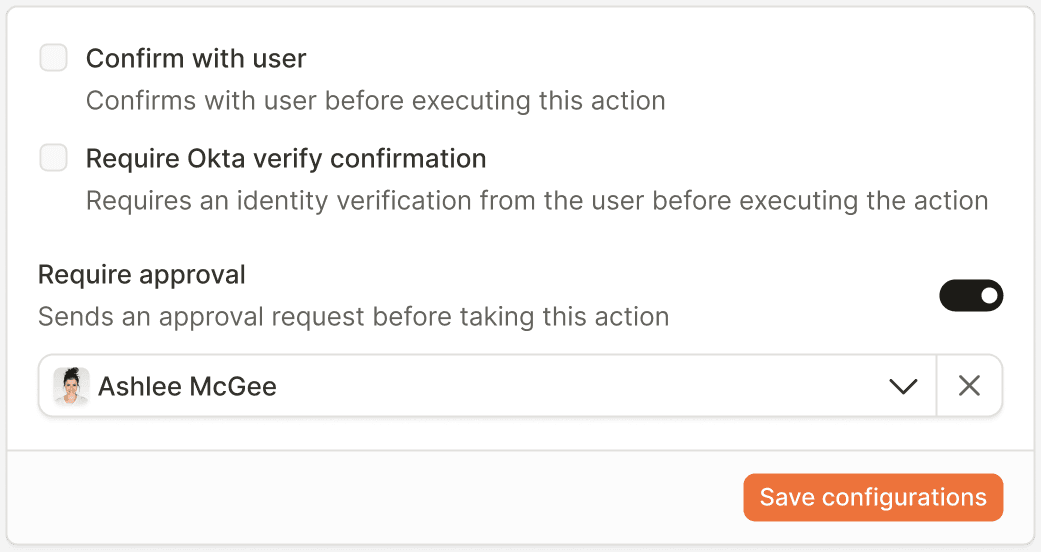
Apply granular controls at every step of an automation. Options include user confirmation before executing actions, Data Verify confirmation for identity verification, and security approval requests before taking actions.
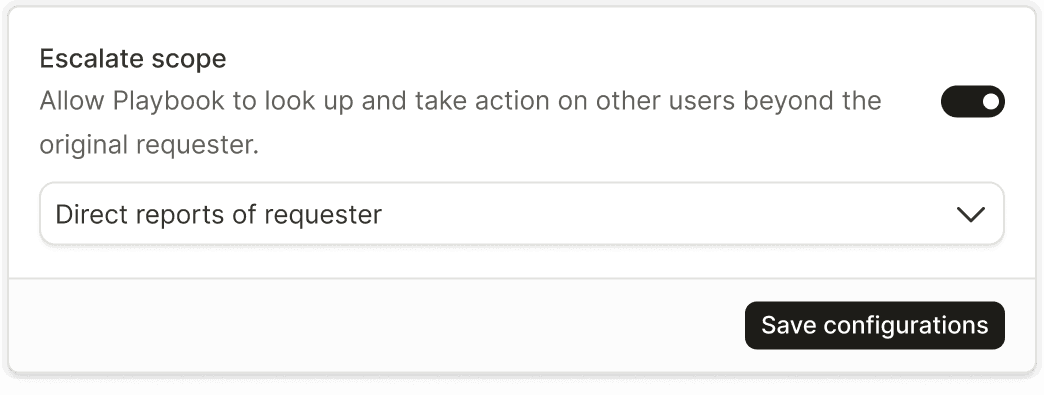
Restrict automations to self-service workflows. By default, automations can perform actions on the requester only. Elevate scopes to empower managers or admins to run flows on behalf of others.
We safeguard your data through rigorous security measures, including SOC 2 Type II certification, continuous threat detection, and routine penetration testing.

SOC 2 Type II certified

HIPAA Compliant
Does Console have access to my data?
Can I control which employees have access to automations?
What happens if someone accidentally triggers a sensitive automation?
How does Console prevent unauthorized actions across our organization?
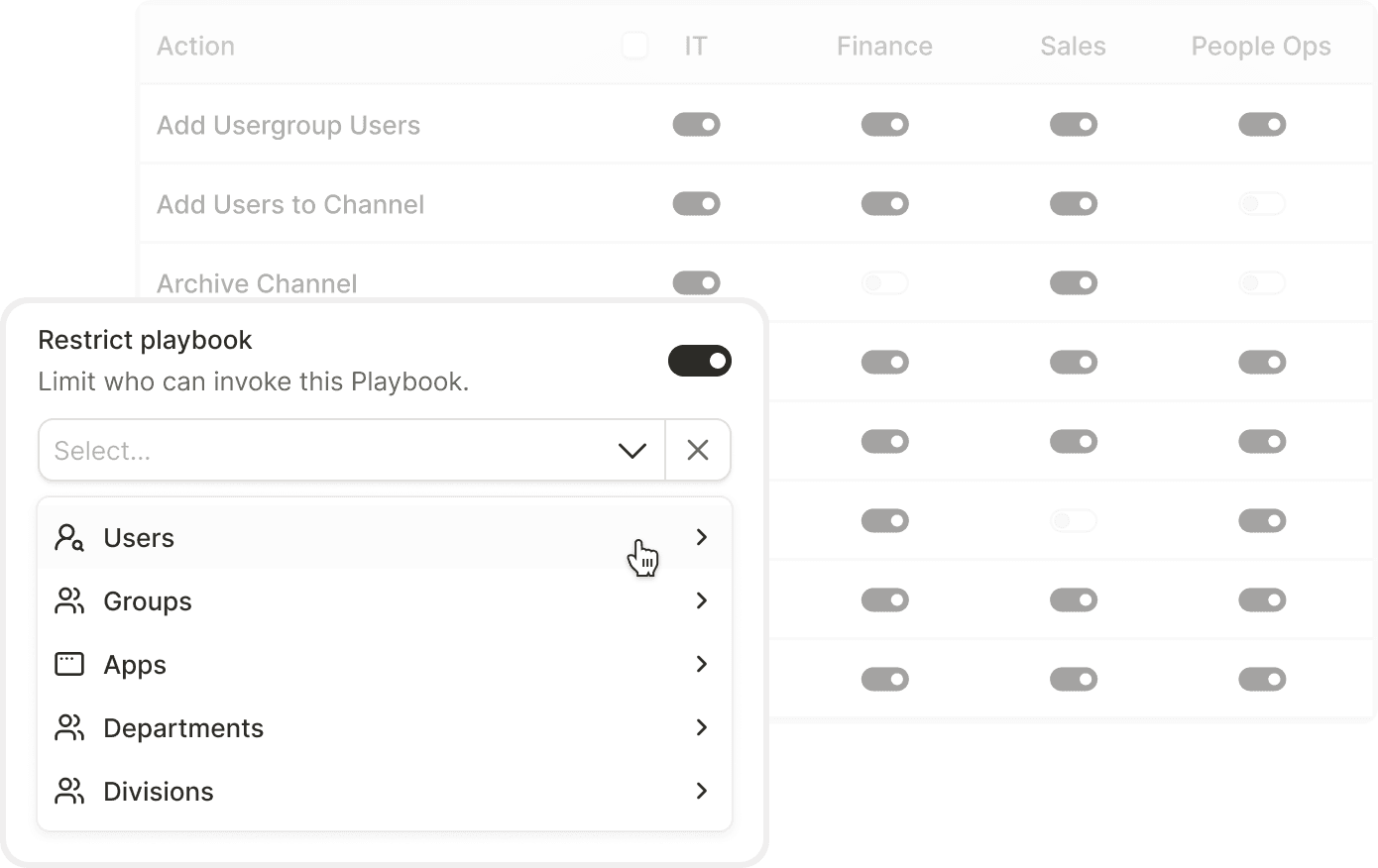
Can I disable certain integrations or actions for specific teams?
Does Console maintain audit logs?
Is Console compliant with healthcare regulations?
How often does Console undergo security testing?
What should I do if I discover a security vulnerability?
Can IT admins support teams without accessing sensitive information?
How does Console ensure automations don't run without oversight?